High-Impact Training for Students
Make a positive impact on learners and campus communities with proven-effective training that supports compliance with federal and state training requirements.
Solutions
Solutions for
K-12
K-12
Learn MoreEducator & Staff Training
Educator & Staff Training
Improve compliance and deliver critical professional development with online courses and management system
Learn moreStudent Safety & Wellness Program NEW
Student Safety & Wellness Program
Keep students safe and healthy with safety, well-being, and social and emotional learning courses and lessons
Learn moreProfessional Growth Management
Professional Growth Management
Integrated software to manage and track evaluations and professional development and deliver online training
Learn moreAnonymous Reporting & Safety Communications
Anonymous Reporting & Safety Communications
Empower your school community to ask for help to improve school safety and prevent crises before they occur
Learn moreIncident & EHS Management
Incident & EHS Management
Streamline safety incident reporting and management to improve safety, reduce risk, and increase compliance
Learn moreHigher Education
Higher Education
Learn MoreStudent Training
Student Training
Increase safety, well-being, and belonging with proven-effective training on critical prevention topics
Learn moreFaculty & Staff Training
Faculty & Staff Training
Create a safe, healthy, and welcoming campus environment and improve compliance with online training courses
Learn moreCampus Climate Surveys
Campus Climate Surveys
Simplify VAWA compliance with easy, scalable survey deployment, tracking, and reporting
Learn moreAnonymous Reporting & Safety Communications
Anonymous Reporting & Safety Communications
Empower your faculty, staff, and students to take an active role in protecting themselves and others
Learn moreIncident & EHS Management
Incident & EHS Management
Streamline safety incident reporting and management to improve safety, reduce risk, and increase compliance
Learn moreManufacturing
Manufacturing
Learn MoreSafety Training NEW
Safety Training
Elevate performance and productivity while reducing risk across your entire organization with online training.
Learn moreIndustrial Skills Training NEW
Industrial Skills Training
Close skills gap, maximize production, and drive consistency with online training
Learn morePaper Manufactuing Training
Paper Manufactuing Training
Enhance worker expertise and problem-solving skills while ensuring optimal production efficiency.
Learn moreHR & Compliance
Provide role-specific knowledge, develop skills, and improve employee retention with career development training.
Learning Management System (LMS)
Learning Management System (LMS)
Assign, track, and report role-based skills and compliance training for the entire workforce
Learn moreEHS Management
EHS Management
Track, Analyze, Report Health and Safety Activities and Data for the Industrial Workforce
Learn moreSafety Communication
Safety Communication
Enhance the safety for the industrial workforce with two-way risk communications, tools, and resources
Learn moreFire Departments
Fire Departments
Learn MoreTraining Management
Training Management
A training management system tailored for the fire service--track all training, EMS recerts, skill evaluations, ISO, and more in one place
Learn moreCrew Shift Scheduling
Crew Shift Scheduling
Simplify 24/7 staffing and give firefighters the convenience of accepting callbacks and shifts from a mobile device
Learn moreChecks & Inventory Management
Checks & Inventory Management
Streamline truck checks, PPE inspections, controlled substance tracking, and equipment maintenance with a convenient mobile app
Learn moreExposure and Critical Incident Monitoring NEW
Exposure and Critical Incident Monitoring
Document exposures and critical incidents and protect your personnels’ mental and physical wellness
Learn moreEMS
EMS
Learn MoreTraining Management and Recertification
Training Management and Recertification
A training management system tailored for EMS services—EMS online courses for recerts, mobile-enabled skill evaluations, and more
Learn moreEMS Shift Scheduling
EMS Shift Scheduling
Simplify 24/7 staffing and give medics the convenience of managing their schedules from a mobile device
Learn moreInventory Management
Inventory Management
Streamline vehicle checks, controlled substance tracking, and equipment maintenance with a convenient mobile app
Learn moreWellness Monitoring & Exposure Tracking NEW
Wellness Monitoring & Exposure Tracking
Document exposures and critical incidents and protect your personnels’ mental and physical wellness
Learn moreLaw Enforcement
Law Enforcement
Learn MoreTraining and FTO Management
Training and FTO Management
Increase performance, reduce risk, and ensure compliance with a training management system tailored for your FTO/PTO and in-service training
Learn moreEarly Intervention & Performance Management
Early Intervention & Performance Management
Equip leaders with a tool for performance management and early intervention that helps build positive agency culture
Learn moreOfficer Shift Scheduling
Officer Shift Scheduling
Simplify 24/7 staffing and give officers the convenience of managing their schedules from a mobile device
Learn moreAsset Mangagement & Inspections
Asset Mangagement & Inspections
Streamline equipment checks and vehicle maintenance to ensure everything is working correctly and serviced regularly
Learn moreEnergy
Learn MoreSafety Training
Safety Training
Elevate performance and productivity while reducing risk across your entire organization with online training.
Learn moreEnergy Skills Training
Energy Skills Training
Empower your team with skills and safety training to ensure compliance and continuous advancement.
Learn moreHR & Compliance
Provide role-specific knowledge, develop skills, and improve employee retention with career development training.
Learning Management System (LMS)
Learning Management System (LMS)
Assign, track, and report role-based skills and compliance training for the entire workforce
Learn moreEHS Management
EHS Management
Track, analyze, report health and safety activities and data for the industrial workforce
Learn moreLone Worker Safety
Lone Worker Safety
Enhance lone worker safety with two way risk communications, tools, and resources
Learn moreGovernment
Learn MoreFederal Training Management
Federal Training Management
Lower training costs and increase readiness with a unified system designed for high-risk, complex training and compliance operations.
Learn moreMilitary Training Management
Military Training Management
Increase mission-readiness and operational efficiency with a unified system that optimizes military training and certification operations.
Learn moreLocal Government Training Management
Local Government Training Management
Technology to train, prepare, and retain your people
Learn moreFire Marshall Training & Compliance
Fire Marshall Training & Compliance
Improve fire service certification and renewal operations to ensure compliance and a get a comprehensive single source of truth.
Learn moreFire Academy Automation
Fire Academy Automation
Elevate fire academy training with automation software, enhancing efficiency and compliance.
Learn morePOST Training & Compliance
POST Training & Compliance
Streamline your training and standards operations to ensure compliance and put an end to siloed data.
Learn moreLaw Enforcement Academy Automation
Law Enforcement Academy Automation
Modernize law enforcement training with automation software that optimizing processes and centralizes academy information in one system.
Learn moreEHS Management
EHS Management
Simplify incident reporting to OSHA and reduce risk with detailed investigation management.
Learn moreArchitecture, Engineering & Construction
Architecture, Engineering & Construction
Learn MoreLearning Management System (LMS)
Learning Management System (LMS)
Ensure licensed professionals receive compliance and CE training via online courses and learning management.
Learn moreOnline Continuing Education
Online Continuing Education
Keep AEC staff licensed in all 50 states for 100+ certifications with online training
Learn moreTraining
Training
Drive organizational success with training that grows skills and aligns with the latest codes and standards
Learn moreEHS Management
EHS Management
Track, Analyze, Report Health and Safety Activities and Data for AEC Worksites
Learn moreHR & Compliance
HR & Compliance
Provide role-specific knowledge, develop skills, and improve employee retention with career development training.
Safety Communication
Safety Communication
Enhance AEC workforce safety with two-way risk communications, tools, and resources
Learn moreCasino
Casino
Learn MoreAnti-Money Laundering Training
Anti-Money Laundering Training
Reduce risk in casino operations with Title 31 and Anti-Money Laundering training compliance
Learn moreEmployee Training
Employee Training
Deliver our leading AML and casino-specific online courses to stay compliant with national and state standards
Learn moreLearning Management System (LMS)
Learning Management System (LMS)
Streamline training operations, increase employee effectiveness, and reduce liability with our LMS for casinos
Learn moreEHS Management
EHS Management
Simplify incident reporting to OSHA and reduce risk with detailed investigation management
Learn moreEmployee Scheduling
Employee Scheduling
Equip your employees with a mobile app to manage their schedules and simplify your 24/7 staff scheduling
Learn moreIndustries
Industry
Resources

Resource Center
Expert insights to boost training
Resource type
Course Catalogs
Company
Course Center
Strengthen your safety, well-being, and inclusion initiatives with high-impact training and higher education software solutions for students, faculty, and staff.





higher retention rates among CPN Seal of Prevention recipients
of schools see increases in bystander skills
decrease in alcohol-related harms
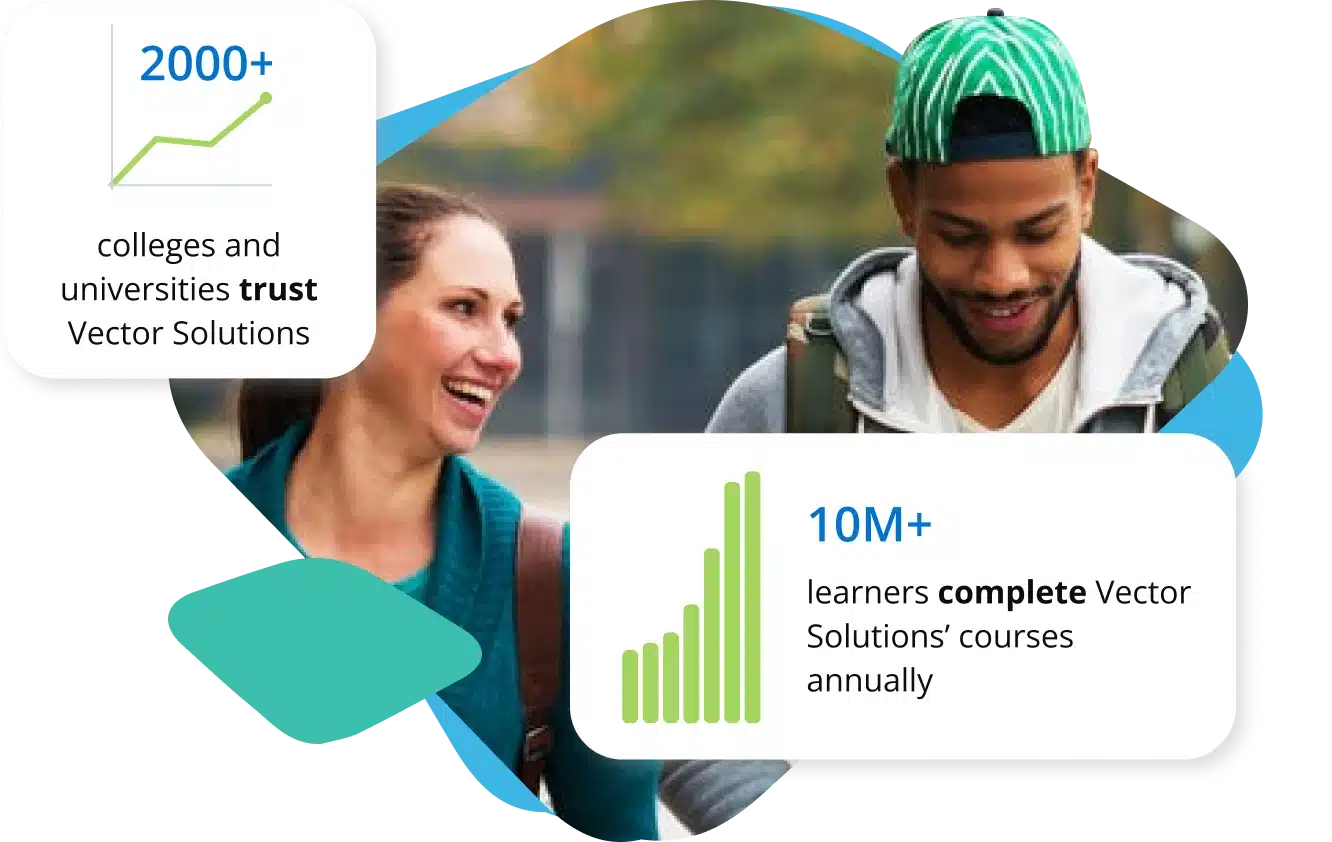
colleges and universities trust Vector Solutions
learners complete Vector Solutions’ courses annually
Make a positive impact on learners and campus communities with proven-effective training that supports compliance with federal and state training requirements.

Improve workplace culture, enhance employee performance, and help meet federal and state training compliance requirements with evidence-based training.

Comply with the new VAWA requirements, streamline climate survey deployment, and integrate with the Vector LMS to analyze all campus-level data in one place.

Surface early warning insights to help prevent safety and security incidents, empower your faculty, staff, and students to ask for help, and quickly deliver safety information at scale.

Strengthen campus safety and address OSHA compliance requirements with a powerful platform to help you manage incidents, investigations, hazards, inspections, and more.
Elevate your commitment to prevention and safety with proven training and software solutions for students, faculty, and staff.
Elevate your commitment to prevention and safety with proven training and software solutions for students, faculty, and staff.
Request a Demo
Empower students to make safe and healthy decisions with proven-effective courses.
Explore Courses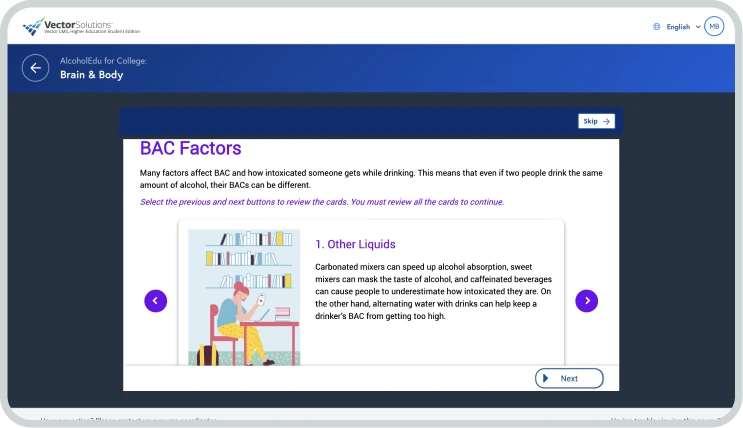
Prepare students to develop healthy relationships, prevent harassment and assault, and support survivors.
Explore Courses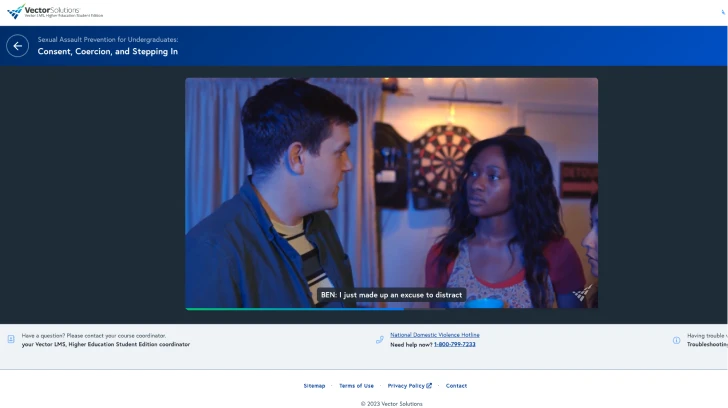
Increase inclusive language, attitudes, and behaviors among students with courses that make a difference.
Explore Courses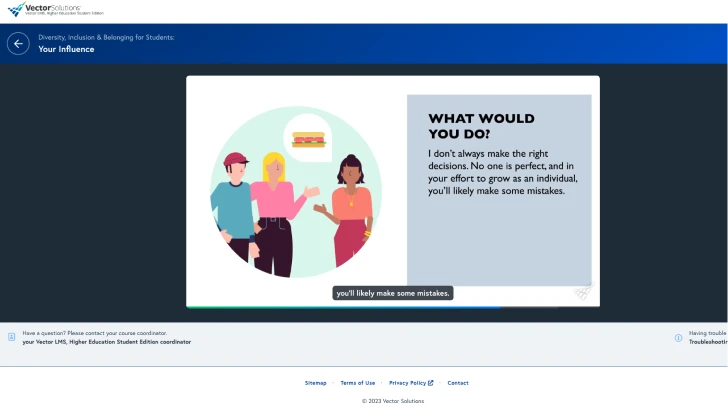
Equip students with essential skills to maintain optimal mental health and wellness.
Explore Courses
Support college athletes with customized training on safety, well-being, and inclusion topics.
Explore Courses
Prepare students for a successful transition to the workplace with powerful training on key life, leadership, and social skills necessary to be successful.
Explore Courses
Empower fraternity and sorority members with prevention, well-being, and safety training to build safer, stronger organizations.
Explore Courses
Foster a safe, accepting campus environment and help comply with Title IX and Clery Act requirements.
Explore Courses
Build interpersonal skills and increase inclusive language, attitudes, and behaviors.
Explore Courses
Meet the needs of athletic staff with customized training on safety, well-being, and inclusion topics.
Explore Courses
Build faculty and staff skills on topics like HIPAA, FERPA, hiring considerations, and employee performance.
Explore Courses
Mitigate human error and address the personal and physical security aspects of institutional safety.
Explore Courses
Address the people-oriented aspects of safety, such as substance misuse and health emergencies.
Explore Courses
Implement valuable training for facility and asset maintenance, including basic facilities skills and hazard communication.
Explore Courses
Train your team to safely perform preventive maintenance tasks and corrective repairs on your campus.
Explore Courses
Empower faculty, staff, and students with relevant content and valuable strategies embedded in courses specifically designed for higher education.
Evaluated in nine peer-reviewed journals, our courses are proven to positively impact behavior.
Spend less time on tedious administrative tasks thanks to intuitive features, such as analytics and reporting, customizations, and more!




“We chose to partner with Vector Solutions because their employee and student training solution was direct and specific to our needs without trying to sell us additional solutions outside our request. In addition, we were promised excellent client support and they delivered.”
The University of Central Arkansas
Director of Professional Development and Training
Read the customer story
“If another Higher Education administrator asked me about the Vector LMS,, my response would be...what are you waiting for?"
The University of Mary
Director of Human Resources and Title IX Coordinator
Read the customer story
“Vector Solutions is really valuable to me from my perspective as a preventionist and I really appreciate all the work that you do to make sure the content is updated and looks new.”
St. Mary’s College of Maryland
Title IX Investigator and Prevention Specialist
Read the customer story




Vice President, Education Strategy
25 years in higher education

Education Strategy Lead
25 years in higher education

General Manager, Education
15 years in higher education

Higher Education Sector Manager
15 years in higher education

Research Lead
11 years in higher education
Tackle the issues that matter most to higher education institutions and organizations with help from Vector Solutions’ Campus Prevention Network (CPN). CPN provides access to tools, resources, and insights to advance your campus safety, well-being, and inclusion initiatives and drive lasting, large-scale change.
Empower students to make safe and healthy decisions.
Emphasize the importance of overall well-being.
Build a campus community of belonging and respect.




June 12, 2023 2 min read

August 7, 2023 3 min read

January 19, 2023 8 min read





September 26, 2023

September 19, 2023

September 7, 2023
March 15, 2023



July 25, 2023

February 23, 2023

January 24, 2023

April 19, 2022

Our expert-authored online training and K-12 training platform are specifically designed for educators, staff, and students.
Our expert-authored online training and K-12 training platform are specifically designed for educators, staff, and students.
Our expert-authored online training and K-12 training platform are specifically designed for educators, staff, and students.
Our expert-authored online training and K-12 training platform are specifically designed for educators, staff, and students.
